(Note, this story is not related to – or even close to being descriptive of – any employer I've worked at, it was simply inspired by a personal friend, and honestly doesn't reflect any job I've been in, but it does remind me of a situation I've actually heard of, and I just thought this exaggeration would be funny)
“Well, well. If it isn't the man with a plan. Working hard and still up at...”, the tick pauses to look at its watch.
“Past 3AM!?”, it shouts in surprise.
“B-boss. I'm over here, working hard! I just wanna make you proud! This night's off company time, all on me”, the pale and shriveled up little man uttered, as he shifted uncomfortably.
“Okay... Nice work, son.” The microscopic tick, almost too small to see with the human eye, beamed with joy at its employee, a rare occurrence.
What a sucker, it thought.
Immediately, the tick regretted showing any positive emotion, remembering that an employee concerned for their job security is a productive employee.
Tch. What am I doing, smiling? Gotta keep them guessing. That's why I don't use turn signals when I change lanes.
It returned to a resting frown – an expression that would reduce the effects of aging and wrinkles on it's smooth, lacquer and blood-stained exoskeleton.
Perhaps I should take the opportunity to add a fourth project on this guy's shoulders, he seems like he might actually enjoy it, thought the tick, knowing full well the bags under the man's eyes were darkening with every passing month.
The pale man stayed silent for a second, then became even more visibly awkward.
He sat up in his chair, as if to prepare himself to exorcise a painful sentence out of his extra-large breathing hole.
“Ah? Well, I hope you keep up the good performance”, said the tick, beginning to contort the upper half of its polished husk away from the man.
“Wa-wait, pl-please. If you have a minute, sir.”
Oh dear god. The tick's mind began to race. He's going to say he got a job offer and wants to leave. Of course. I've been working him too hard, putting on too much pressure, and now I'm losing one of my most productive assets. I'll tell him he can't leave, that it's going to complicate his 401k situation, that his wife and kid are going to be put in financial trouble if that new company starts doing budget cuts.
Aha, I'll remind him the economy is bad. When isn't it bad when you make under $40k? Plus, he can't really ever leave after working here for so many years, his heart isn't in it. Bite into him. Tell him we have a place for him here, that he belongs. Wait. Does he even have a wife and kid? Isn't this guy in his late 40s and living in a rental apartment more than an hour away? No way, that's right. He's single and has been here for at least 5 years. He'll do whatever I say.
“Now, listen her-”, the tick stops, realizing it's entirely forgotten the name of this employee.
Was it... Curtis? Clyde? ...Richard?
“Yes, s-sir?”, the jaunt-faced man stuttered.
“No, go on...”, urged the tick.
“W-well. I've b-been at the company f-for two decades... and...”
Holy crap. Who in their right mind would limit their career prospects like that after 2020? This guy is so painfully loyal and gullible, I'm so ready to reel him back in once he tells me he's leaving. He's younger than me and he's already balding, I'll bring that up when I tell him there's two kinds of people in this world: leaders, and followers.
Baldness really breaks down their ego, makes them crawl back to you. Lets you latch onto them for longer, before they give out. Worst case, I'll guilt trip him into a 6 week notice. After that, they might drop him at the new place, and he might stay here after all. Really ram it into him for that next month and a half that he's gotta stay.
“A-and... so... I wa-was hoping... you could find it in your heart... to give me a promotion! Oh god, I'm sorry... I hope I didn't upset you”, the fragile man pleaded in a dry, raspy voice.
Wow. How can I even try to fathom this shadow of a man?
Permanently helpless. Trapped forever in a rat race. This is exactly the kind of person I want to stay in their exact role forever and never leave. I have to keep him here for the rest of his working life. No, past that. Until he draws his last breath.
“Maybe I should remind you that people are retiring later and later nowadays, things are getting rough in the economy. You shouldn't be making demands like that at a company you've been at for only 20 years.” Throw him against the wall. And then... suck what little bit of light and life behind those eyes are left, until he feels like giving up, and becomes a machine for me.
The tick continued, “You see, your life is going very well. You should be grateful. This company has given you... so, so much.”
The man makes a wide, wrinkled frown as his eyes begin to water.
Oh shit. He's going to cry. I overestimated his resolve, his character, what little sense of individuality he had left. He's already shattered, and he was trying to pick up the pieces, and his hands are covered in blood from all the cuts into his soul. His delicious, succulent blood. Let me reel this back in. Make him smile. Get his hopes up, make some shit up.
“And... you've been a loyal employee. I respect a man who works to fill in the shoes of a short-staffed team of seven men down to one. Maybe I'll even consider it, in a year or two”, the tick says.
Psh. Yeah, in a year or two, the tick thinks to itself, when I'm going to scalp him from this company, after I leave with him to make my own startup. After he builds out the whole product, he'll be so hysterically confused when venture capitalists come in and lay him off to cut down on costs.
I'll be off having exited shortly before, landing with my golden parachute onto a yacht filled with 47 virgins like those funny cube worshippers dream they'd have.
The man has a glow of happiness come over him. A wide smile of joy not often seen in that office spreads across his face.
“S-sir! Thank-”, he stops to sniffle, “...thank you for y-your consideration!”
What a stupid grin. Shit, ignorance is bliss. It's almost like this is one of the most fulfilling moments of his life.
He stood up for himself once in his life, asked for something, got an empty promise, and still...! That's better than anything he's experienced in probably years. This man does not fuck. This man has no standards, no ambition, no motivation in life but to slave away at this goddamn company for scraps. His happiness is derived from the praise and reactions of his superiors, who'd fire him without a day's notice.
He deserves to be at the bottom of the hierarchy. This is why classes exist. He cannot understand or handle success, wealth, or status. He must be led. He must be shepherded. He must be consumed, when the time of slaughter comes and he grows old. I am his shepherd. I lead him to his death.
The man is still beaming, smiling, exuberantly. “I'll stay all night to finish this sir, you can count on me!”
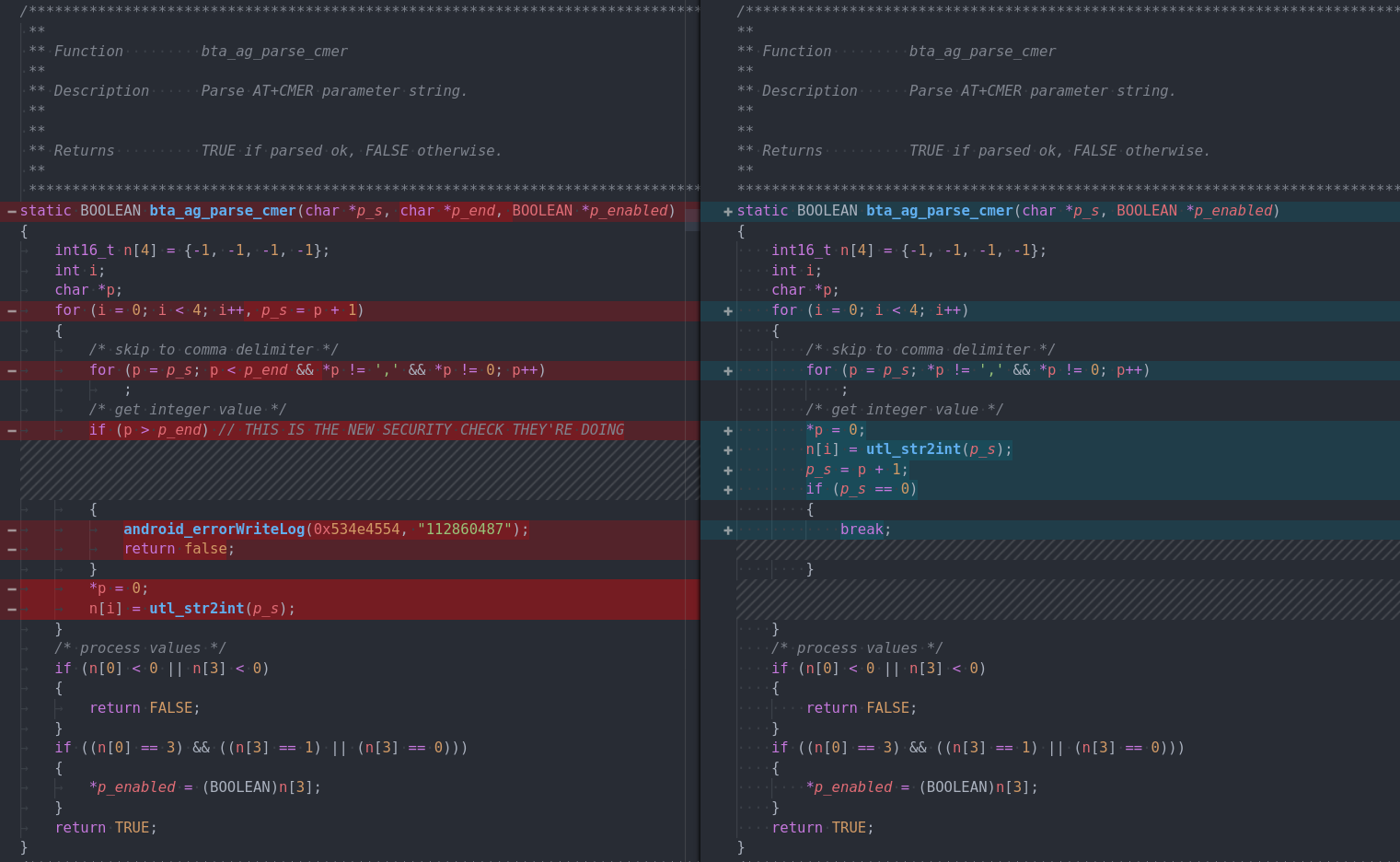
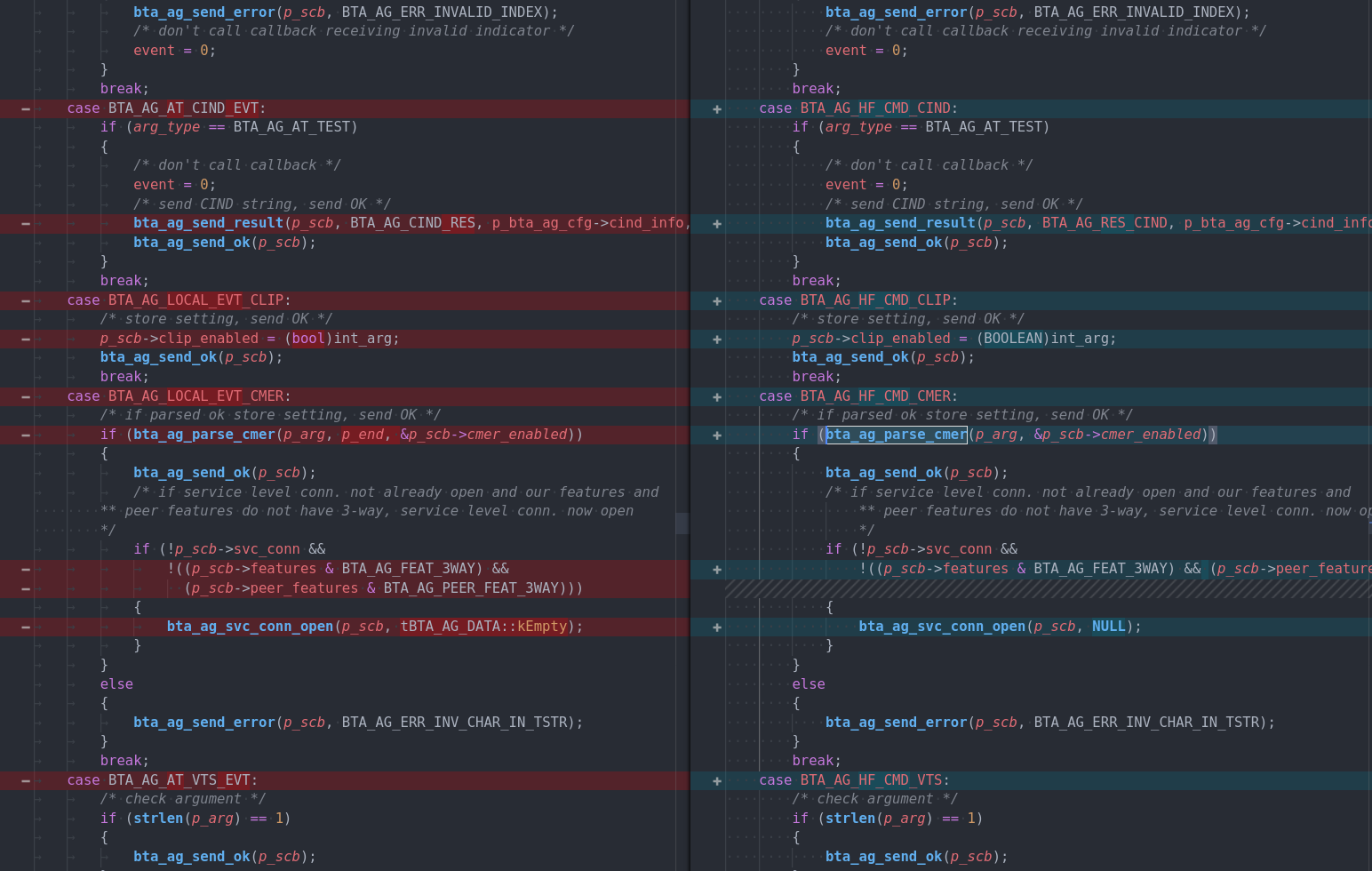
No, he doesn't even realize I'm a dictator in his life, that I'm controlling his financial well-being. Employees really think they're the ones in control, somehow. They don't realize the situation they're in at all is that of a parasite and a host.
I am a tick, slowly drinking away at his blood, taking everything out of him, sucking him dry for what he's got.
He's compromising with a tick he found on himself.